n00bs CTF Level 6
| Link: Webpage | Points: 60 |
Useful Tools: wireshark |
Tags: beginner network |
Show Solution …
The Challenge
At the start of the level, we are prompted to download the file sharkfin.pcap. If you have never seen a filetype like this and don’t know what to do with it, tthe filename is a hint for what tool to use. The program Wireshark has a shark fin logo and it is used to open up network packet capture dumps (.pcap). If you didn’t know about Wireshark, a Google search on how to open PCAP files would point you to it.
There is a lot going on in this packet capture; if you are new to Wireshark, what you are seeing can look fairly overwhelming or daunting. If you scroll for a while through all of the packets, you may start to notice that the vast majority of them are HTTPS and encrypted packets. We can’t decrypt these packets without a key, so let’s look at the non-encrypted packets first. The very first packet is UDP and plaintext/readable. If you select it and look at its hex content on the bottom of the screen, you will see a string of hex values.
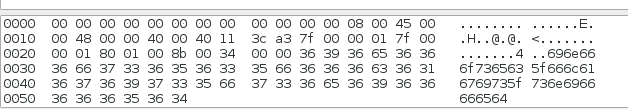
The data that we care about is in the right-most section. See any patterns or key characteristics of those values? You may notice that there are a lot of 6’s and 7’s in there, which is a good indicator that this hex represents ASCII characters (lowercase letters fall in the hex 61-7A range). Take a look at this ASCII table to verify. Let’s try converting those numbers from hex to ASCII and see if we get anything readable.
You can use either an online decoder, a hex editor, or a script to convert this from hex to ASCII. This will result in the flag: infosec_flagis_sniffed
Lessons Learned
The main skill gained here is some proficiency with using Wireshark. Wireshark can look intimidating at first glance, but it won’t take long to get used to working with it. It also has a lot of features for sorting through all those packets, making your analysis job much easier. See other network challenges for more examples of using Wireshark.
The next lesson learned was how to identify hex-encoded ASCII and convert it back to a string. Hex values can be written as just the number 60 or with the prefix 0x, such as 0x60. It really depends on what you are looking at to know which you will see; in the case of this pcap file, it just had the numbers without the prefix. In this case, it is up to you to simply notice that they are hex values (versus decimal), and notice that they are potentially worth investigating. Remember, if you see a lot of numbers in the hex 60-70s back to back, it is probably an ASCII string. Being able to quickly spot patterns like this can save you a lot of time.
Lastly, you gained a fourth decoder/converter for your back-pocket. The base64 and hex decoders will likely be your most-used.
