SHA2017 Junior CTF - Download
We have a network capture of someone downloading something from the internet. Can you find what it is?
| Files: Download | Points: Network 1 |
Useful tools: wireshark tcpdump tshark |
Tags: beginner network |
Show Solution …
This challenge provides a packet capture file for analysis. If you haven’t seen “.pcap” as a file extension before, a quick Google search will point you to using Wireshark to analyze these kinds of files.
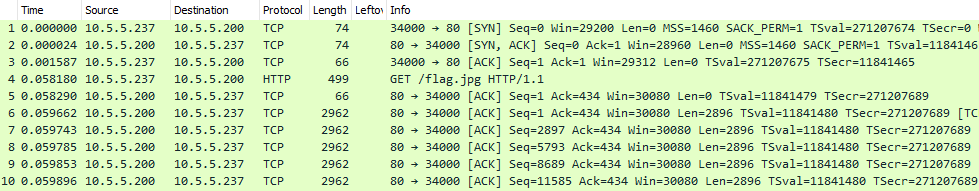
Wireshark can look very overwhelming if you haven’t experienced it before, but you can actually get the hang of it fairly quickly. This is a packet capture where someone was sniffing all network packets going across the wire, and each row in Wireshark represents one of these packets. You can see from the Source and Destination columns that this capture file is just between two IP addresses talking to each other; nothing else was captured. From the Protocol column, we can see that this is mostly HTTP and other TCP traffic. Packet #4 in particular is an HTTP packet for a GET request to flag.jpg, which you can tell from the Info column on the far right. Since the user was requesting a JPG file, you can assume that the TCP packets below this request all make up the data for that JPG.
Luckily, we don’t need to try to reconstruct this image ourselves by somehow taking the data from each packet and gluing it all back together. Wireshark has a great feature that will do this for us. Click on File --> Export Objects --> HTTP
You will see flag.jpg appear in this window. Click Save, and open it up with any image viewer to see the file.

The flag for this challenge is flag{259f1b841eaaa4fcb843d77dcdade55a}
Review & Lessons Learned
Wireshark is a very powerful tool to analyze pcap files. This should always be your first go-to when performing packet analysis. There are many other very useful features that will come in handy for other challenges. Spoiler: Try right clicking that HTTP packet and selecting “Follow –> TCP Stream”
